Kentik Blog
























This week, VMware announced plans to acquire SD-WAN startup VeloCloud. Google released a new Andromeda SDN to reduce its cloud latency. SoftBank, Facebook, Amazon and others made plans to lay a 60-Tbps undersea cable from Juniper. And Energy giant Chevron selected Microsoft as its preferred cloud provider. Those headlines and more after the jump…
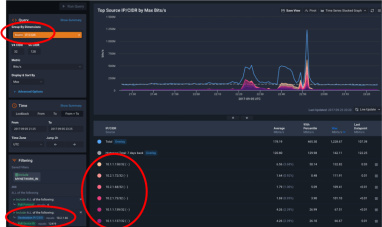
At Kentik, we built Kentik Detect, our production SaaS platform, on a microservices architecture. We also use Kentik for monitoring our own infrastructure. Drawing on a variety of real-life incidents as examples, this post looks at how the alerts we get — and the details that we’re able to see when we drill down deep into the data — enable us to rapidly troubleshoot and resolve network-related issues.
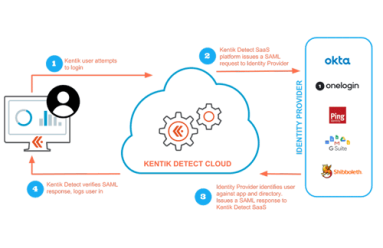
As security threats grow more ominous, security procedures grow more onerous, which can be a drag on productivity. In this post we look at how Kentik’s single sign-on (SSO) implementation enables users to maintain security without constantly entering authentication credentials. Check out this walk-through of the SSO setup and login process to enable your users to access Kentik Detect with the same SSO services they use for other applications.
Reports this week suggest a Russian teleco started providing internet connectivity to North Korea. Russia also made headlines for its covert efforts to steal secrets from the NSA. Oracle made a bunch of news with its OpenWorld conference this week, including taking aim at AWS. And Google disclosed seven vulnerabilities in DNS’ Dnsmasq software. More headlines after the jump…
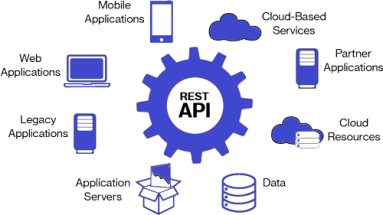
In today’s world of heterogeneous environments and distributed systems, APIs drive synergistic innovation, creating a whole that’s more powerful than the parts. Even in networking, where the CLI rules, APIs are now indispensable. At Kentik, APIs have been integral to our platform from the outset. In this post we look at how partners and customers are expanding the capabilities of their systems by combining Kentik with external tools.
Microsoft, Facebook and teleco provider Telxius announced this week that their high-capacity subsea cable project is complete. A “network issue” in a global flight-booking system caused major airline delays. And an “alarming number” of patched Macs are vulnerable to an issue in the Extensible Firmware Interface. More after the jump…
Cisco Chairman John Chambers announced this week that he will not seek re-election. The networking giant also announced a partnership with Viacom. Meanwhile, Cisco researchers found that the CCleaner malware was targeting at least 18 tech companies. More after the jump…
As the east coast prepares for Hurricane Irma, those with data centers in the storm’s path are also making efforts to avoid interruptions. DDoS attackers took a gamble this week, making a hit on popular online poker site America’s Cardroom. And a debate has up on how CenturyLink’s plans to acquire Level 3 Communications could affect broadband in rural areas. More after the jump…
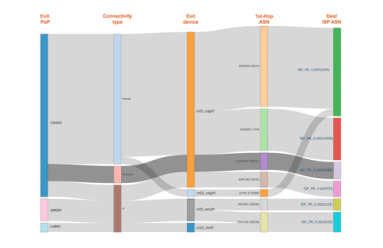
In our latest post on Interface Classification, we look beyond what it is and how it works to why it’s useful, illustrated with a few use cases that demonstrate its practical value. By segmenting traffic based on interface characteristics (Connectivity Type and Network Boundary), you’ll be able to easily see and export valuable intelligence related to the cost and ROI of carrying a given customer’s traffic.
Apple announced two new data centers in Iowa. Cisco made another acquisition. VMware reported a strong quarter. DDoS attacks spiked. Google sped up TCP/IP. And Wired put together an interactive map to show where internet trolls live. More headlines after the jump…